Protect bowser-based work on un-managed Windows Devices - Part 1 Intune App Protection Policies for Edge (The Container Layer)
Historically, safeguarding proprietary information mandated total control over the physical hardware. However, with the shift toward SaaS-based apps and the rise of remote work, the paradigm has moved toward securing the data itself rather than the device. Staff and external partners are no longer restricted to corporate-owned and managed Windows devices, thanks to the robust controls available within Microsoft 365. Organizations can now focus on a versatile strategy that closes visibility gaps without overstepping onto personal or third-party hardware.
Microsoft is bolstering the defensive features within Edge for Business, Entra, Intune, and Purview. Recent enhancements to profile handling and authentication now enable firms to insulate browser-centric tasks on PCs governed by other entities. These advancements synchronize Purview’s real-time data oversight with Intune’s structured deployment frameworks, allowing administrators to deploy a unified security blanket rather than juggling disconnected settings.
This can be best described in form of a two tier management strategy -
The Container Layer (Infrastructure Control)
The first line of defence is the Intune App Protection Policy (APP). This layer focuses on "where" data can go. Edge automatically creates a dedicated work window, separating professional history, passwords, and favourites from personal ones. Because these policies are tied to the Entra ID login, they apply even on devices the company doesn't own.
The Content Layer (Data Intelligence)
While the container sets the rules, Microsoft Purview DLP provides the intelligence. This layer is "content-aware". Purview doesn't just block all copy/pasting; it can be set to block only if the text contains sensitive info, like credit card numbers or internal project names.
One of the biggest advantages is that it works natively in Edge. You don't need to "onboard" the personal device to Purview or install complex agents.
I'll cover the first part in this blog post which is the configuration of Intune App Protection Policy (APP) (The Container Layer).
Let's start with the pre-requisites -
1. Microsoft Intune Plan 1 at a minimum.
2. Microsoft Entra ID Premium 1 (This is optional, but highly recommended, especially if you are implementing Conditional Access)
3. Microsoft Edge version 120 or later.
4. Windows 10/11 (specifically build 19045.3636 / 10.0.22621.2506 or later).
Configure the App Protection Policy (APP)
The APP defines the "walls" of your container by restricting how data moves in and out of the Edge work profile.
1. Navigate to Microsoft Intune admin center.
2. Go to Apps > App protection policies > Create policy > Windows.
3.Target Apps: Specifically select Microsoft Edge as the targeted application.
4. Data Protection Settings -
Receive data from: All sources OR No sources (as required)
Send org data to: No destinations (recommended)
Allow cut, copy, and paste for: Org data destinations and org data sources (restrict "Cut, copy, and paste" to only occur within the work profile or block it entirely to external apps)
Print org data: Block (recommended)
5. Assign to a user based group. Note: Managed app filters are limited for Windows OS. There is no easy way of differentiating between personal and corporate devices. Since MAM wouldn't apply on a managed Windows device, it is recommended to apply the APP to the same user group as the one used for Conditional Access (Covered later in this post).
Enforce with Conditional Access
This is highly recommended as the container isn't locked until you require its use via a Microsoft Entra Conditional Access Policy.
Configure the following values:
Select the relevant group of users meant to be targeted for CA policy. Example - Contractors
Select All resources.
Select Windows as the device platform.
Select Browser & Exchanged ActiveSync clients as these are the only apps supported for Windows APP.
Exclude Intune managed devices.
Set the policy to "Require app protection policy" for Windows platforms.
End Result
When the target user tries to access corporate data from a personal device using an unmanaged Edge profile, they will be blocked and redirected to sign into the protected Edge work profile.
Select Yes to allow the device to register with Entra ID. Note: Administrators can enable the “Disable MDM enrollment when adding work or school account” setting to block the prompt for device enrollment during the account registration flow.
Sign-in events in Entra can be checked to validate the enforcing of the correct CA policy.
When a user tries to copy data from a managed browser session to an unmanaged space, the access will be restricted.
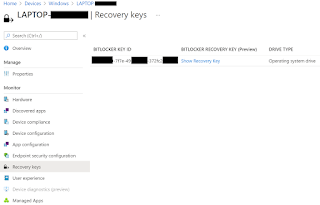
APP compliance can be checked in Intune for validation as well.
Final thoughts..
This unified approach to browser-based security for unmanaged Windows devices (BYOD) uses Edge for Business as the primary workspace. By layering Intune and Purview, you shift security from the device itself to the work context, ensuring corporate data remains protected without needing full device management.
That wraps up Part 1! We've successfully built our security container. In Part 2, we’ll explore the Content Layer to see how to protect the actual data inside. This is a critical step in my opinion as even in a managed browser session, data leaks can still happen. Especially if you don't have the right data security controls in place. Stay tuned!





















Comments
Post a Comment